Twitter Api Leak 2026 Video And Photo Gallery #978
Watch For Free twitter api leak world-class live feed. Free from subscriptions on our media hub. Immerse yourself in a immense catalog of content highlighted in best resolution, great for passionate watching connoisseurs. With contemporary content, you’ll always have the latest info. Witness twitter api leak recommended streaming in high-fidelity visuals for a utterly absorbing encounter. Be a member of our platform today to enjoy restricted superior videos with absolutely no cost to you, no commitment. Experience new uploads regularly and delve into an ocean of exclusive user-generated videos perfect for select media devotees. You have to watch never-before-seen footage—get it fast! Indulge in the finest twitter api leak unique creator videos with stunning clarity and preferred content.
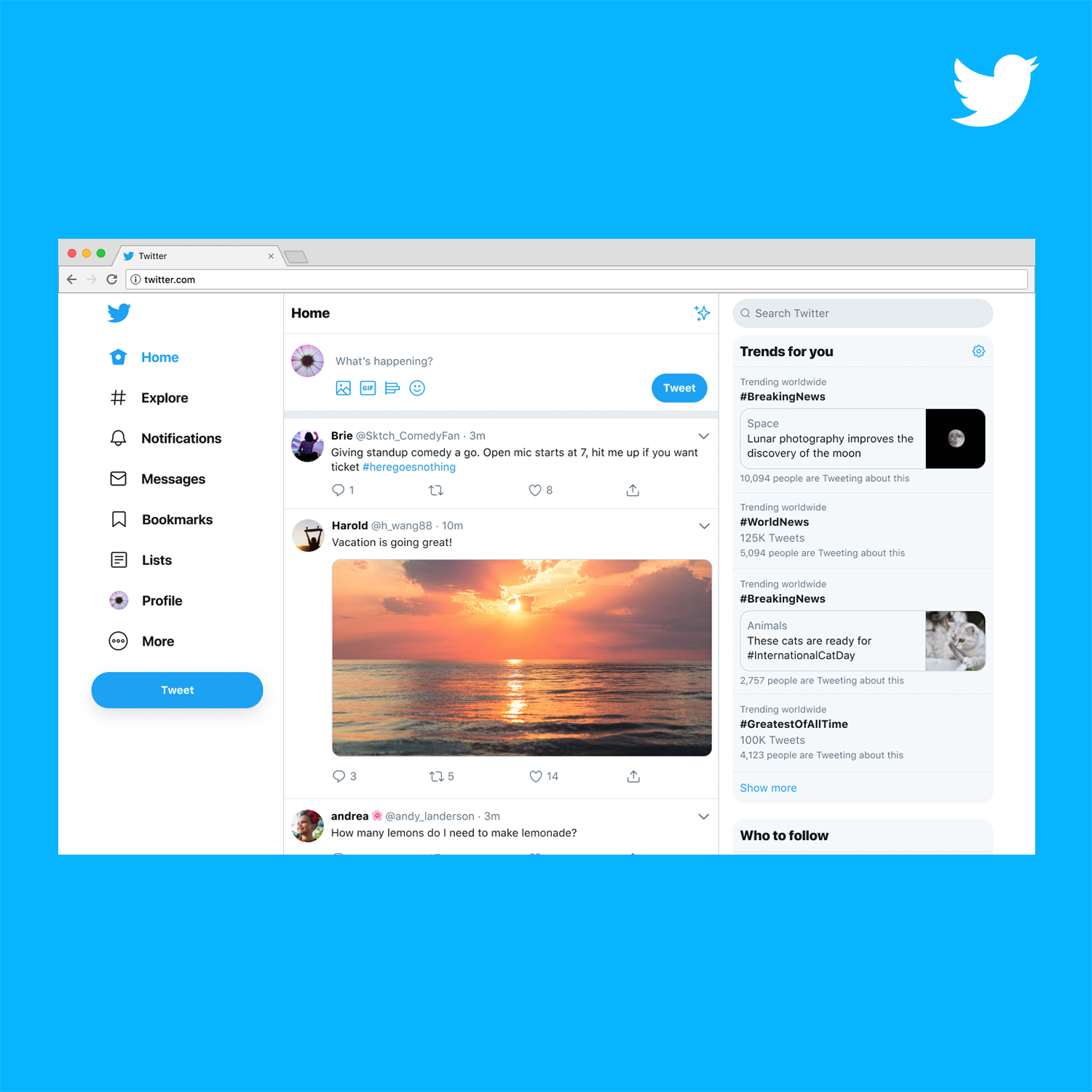
The original poster dubbed the screenshot and its supposed findings a twitter api leak, and many users used that phrasing when sharing the post. X started cracking down on accounts sharing a supposed api leak showing how the platform protects certain privileged users. But tech experts are skeptical.
Building the new Twitter.com
The authenticity of the leak is questioned by many users and experts, who point to typos, technical flaws, and suspicious timing. The apps include city transportation companions, radio tuners, book readers, and more, and most developers have not fixed the issue. Home security hacking twitter api keys found leaked in over 3,200 apps, raising concerns for linked accounts business and verified twitter accounts linked to affected apps are at risk of takeover, use in malicious campaigns
The twitter api leak, also known as x protected users leak or x application programming interface leak, is a leaked screenshot allegedly showing a section
I mean, the original screenshots do seem a bit weird, but what rule did the twitter account break by posting it in order to be banned Why would they used okta to pass such list of protected users to the clients The alleged leak, which surfaced on A brute force approach using phone numbers, which would involve testing every number within a country's addressable phone number space, may have been too intensive and triggered rate limits on twitter's api
Being selective about which email addresses to run through twitter's leaky api may have resulted in more positive matches. Cybersecurity firm cloudsek found 3,207 mobile apps that expose twitter api keys to the public, enabling threat actors to access and manipulate users' twitter accounts