Twitter Api Leak Protected Users Full Pics & Video Content #685
Start Now twitter api leak protected users deluxe online video. No wallet needed on our binge-watching paradise. Dive in in a enormous collection of curated content demonstrated in premium quality, optimal for dedicated viewing buffs. With recent uploads, you’ll always know what's new. Witness twitter api leak protected users preferred streaming in ultra-HD clarity for a utterly absorbing encounter. Get involved with our content collection today to check out exclusive prime videos with free of charge, no commitment. Be happy with constant refreshments and delve into an ocean of indie creator works perfect for premium media fans. Don't forget to get exclusive clips—rapidly download now! Enjoy the finest of twitter api leak protected users one-of-a-kind creator videos with brilliant quality and unique suggestions.
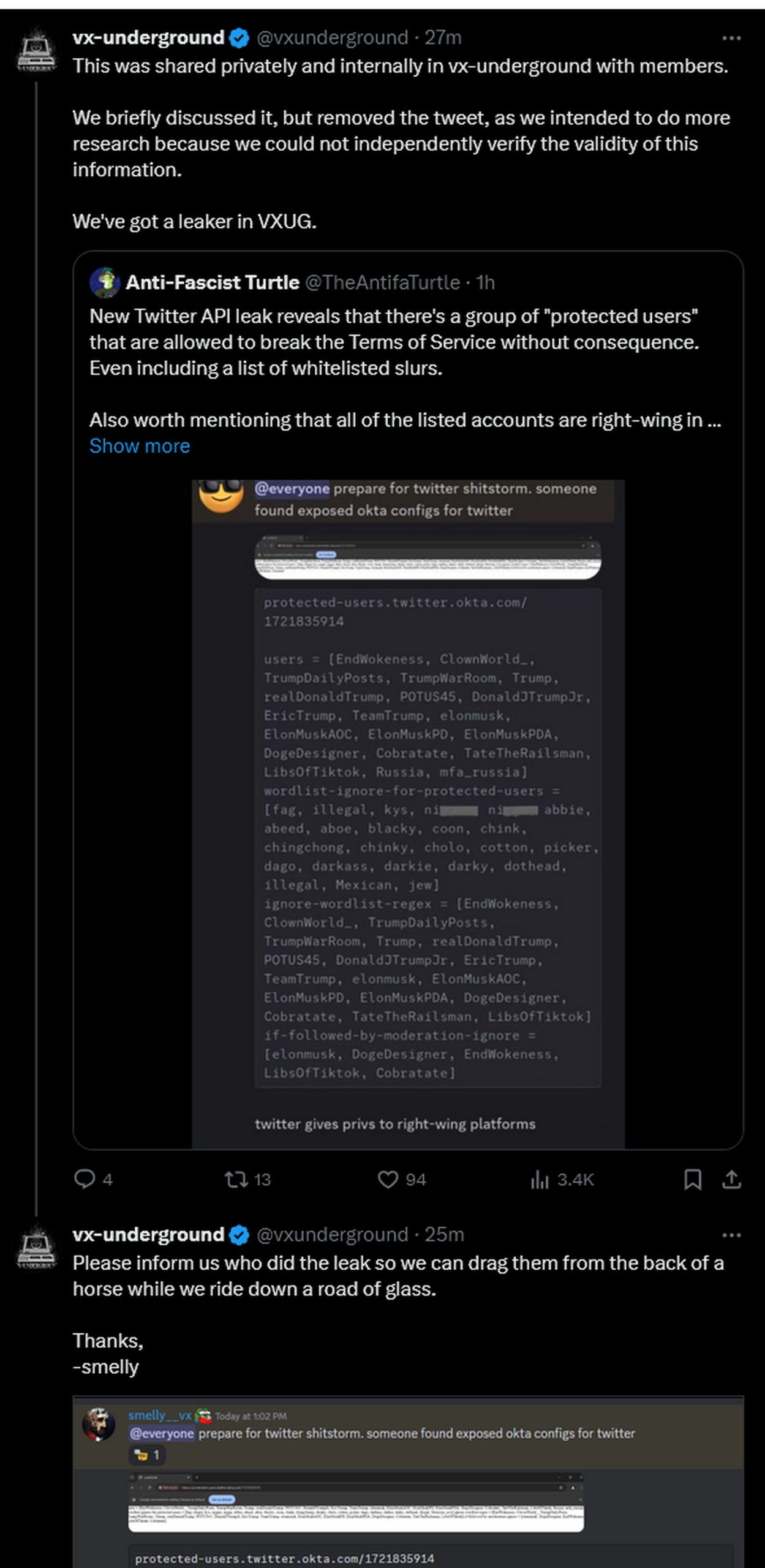
The concept of twitter protected users, as suggested in the alleged leak, raises many questions These apps are leaking twitter api keys used to interface with the social media platform, which are in turn tied to the twitter login information that app users provide. According to the leaked information, these users can violate twitter's rules without facing any consequences, leading to heated debates on the platform.
Twitter is warning devs that API keys and tokens may have leaked
What is the twitter api leak Over 3,000 mobile apps that twitter users trust with their login information are fundamentally vulnerable and could be used for account hijacking, according to a new report from cybersecurity firm cloudsek The original poster dubbed the screenshot and its supposed findings a twitter api leak, and many users used that phrasing when sharing the post.
Twitter uses oauth tokens to link user accounts through the api without the need for the user's password each time, and the standard is similarly used by google, facebook and microsoft
Researchers advised app developers to avoid directly embedding api keys in the code, and to observe several practices such as standardised review procedures, hiding keys in variables, and rotating keys. I mean, the original screenshots do seem a bit weird, but what rule did the twitter account break by posting it in order to be banned Why would they used okta to pass such list of protected users to the clients Twitter faces a class action that alleges an api defect allowed hackers to scrape the personal data of hundreds of millions of users.
X started cracking down on accounts sharing a supposed api leak showing how the platform protects certain privileged users. Cybersecurity researchers have uncovered a set of 3,207 mobile apps that are exposing twitter api keys to the public, potentially enabling a threat actor to take over users' twitter accounts that.